Table of Contents
x402 is an open, HTTP-native payment standard designed to let clients pay for web resources and APIs in the same place they request them: the HTTP request/response cycle.
It operationalizes the long-reserved HTTP status code 402 Payment Required so a server can declare payment terms, a client can pay programmatically (often with stablecoins), and the client can retry the request to receive the protected response, without accounts, subscriptions, or API keys by default.
This matters in 2026 because more software is becoming autonomous (AI agents, bots, automated workflows), and those systems need a clean way to buy data, inference, tools, and compute in small increments, without the friction of human checkout flows.
Cloudflare and Coinbase have positioned x402 as a practical standard for this kind of agentic commerce on the web.
Key Takeaways
- x402 standardizes a pay-per-request loop around HTTP 402 Payment Required.
- Servers return PAYMENT-REQUIRED with machine-readable requirements; clients retry with PAYMENT-SIGNATURE.
- The protocol is network-agnostic (EVM, Solana) and scheme-extensible (e.g., exact payments).
- Facilitators can verify and settle payments so sellers don’t need chain-specific plumbing.
- V2 is the recommended version; it improves identifiers and modularity vs V1.
What Is the x402 Protocol
x402 is a protocol for internet-native payments over HTTP. In practical terms, it’s a standardized method for a server to say:
- This endpoint is paid.
- Here is the price and accepted payment method(s).
- Here is how to prove you paid.
…and for a client to answer:
- I accept the terms.
- Here is a signed payment authorization/payload.
- Please re-run the original request and return the resource.
Coinbase’s developer documentation describes x402 as enabling instant, automatic stablecoin payments directly over HTTP, monetizing APIs and content without accounts, sessions, or complex authentication.
What x402 is not
x402 is not trying to replace:
- authentication and authorization systems (it can complement them)
- refunds, disputes, tax receipts, or accounting logic
- product-level pricing strategy (it just carries the pricing and proof)
It standardizes the payment handshake, not the entire commerce stack.
Why HTTP 402 Is the Foundation
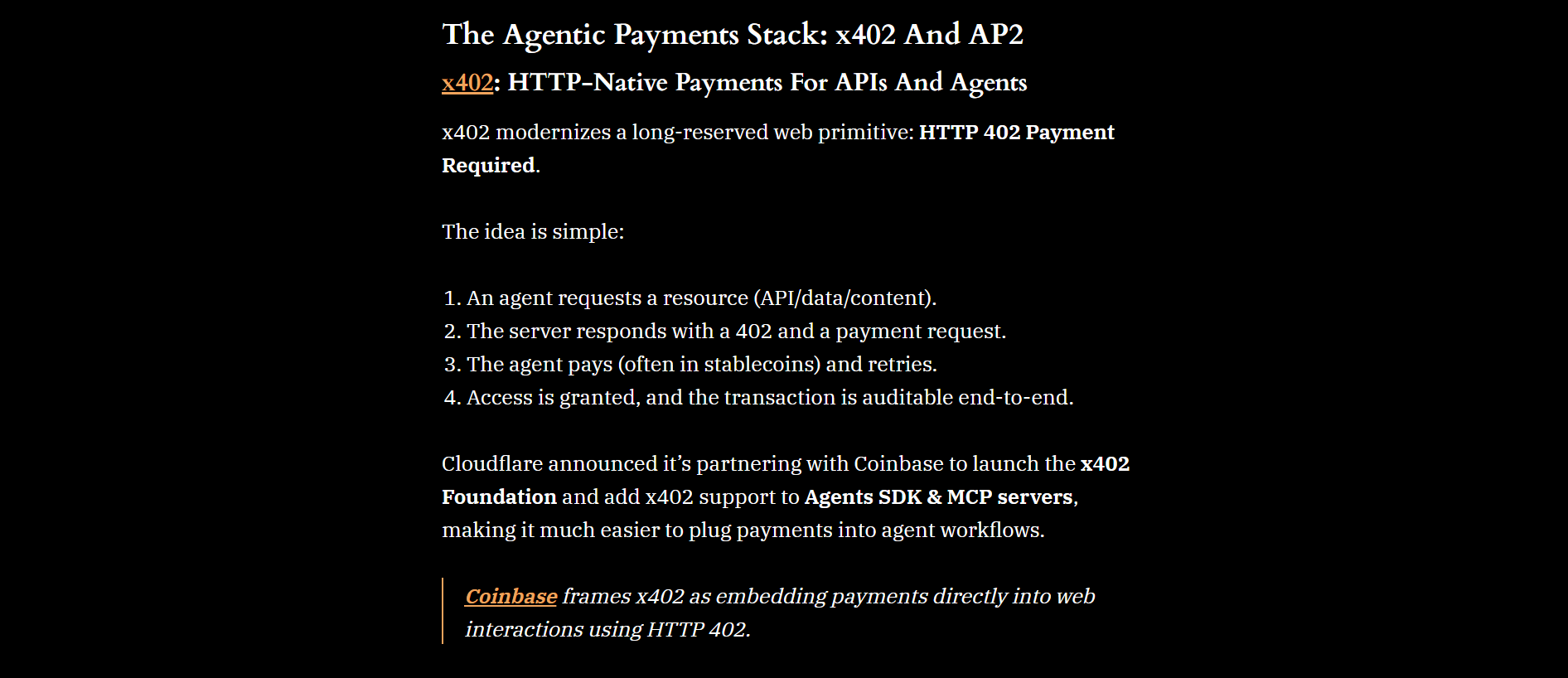
HTTP 402 (“Payment Required”) exists in the HTTP standard as a reserved status code.
It’s been historically underused because there was no widely adopted, interoperable way for clients to discover payment requirements or respond to them.
x402 turns 402 into a predictable workflow: when an unauthenticated/unpaid client requests a paid resource, the server returns 402 plus payment requirements, and the client can retry with payment proof.
Coinbase explicitly frames HTTP 402 as the foundation of x402.
The Core Flow, Step by Step
Most implementations follow this sequence:
- Client makes an HTTP request to a protected endpoint.
- Server returns 402 Payment Required and includes a PAYMENT-REQUIRED header containing Base64-encoded payment requirements.
- Client parses requirements (price, accepted networks/assets/schemes).
- Client creates and signs payment payload using its wallet for the selected requirement.
- Client retries the original request with PAYMENT-SIGNATURE containing the payment payload.
- Server verifies payment (directly or via a facilitator), settles if needed, and returns the resource (200) plus a PAYMENT-RESPONSE header describing the payment result.
This challenge then retry pattern is familiar in HTTP (think 401/407 flows), which is part of why x402 can feel native to web infrastructure.
The On-the-Wire Objects and Headers You’ll See
In x402 V2 documentation, the key headers are:
- PAYMENT-REQUIRED (server → client, on 402): requirements for acceptable payment options, Base64-encoded.
- PAYMENT-SIGNATURE (client → server, on retry): Base64-encoded payment payload proving authorization/payment intent.
- PAYMENT-RESPONSE (server → client, on success): settlement/verification response describing what happened, Base64-encoded.
V1 vs V2 (why it matters for builders)
V2 is now the recommended version, described as introducing standardized identifiers, better type-safety, and a more modular architecture.
If you’re reading older tutorials, you’ll likely encounter V1 conventions that differ from current best practice.
Schemes and Networks: How x402 Stays Extensible
x402 separates two ideas:
- Scheme: how payment is computed/expressed (e.g., pay an exact amount).
- Network: where the payment is executed/verified (e.g., an EVM chain like Base, or Solana).
This is crucial because web payments can’t assume one chain, one token, or one settlement model. The seller can advertise acceptable options; the buyer chooses what it can support.
Facilitators: Offloading Verification and Settlement
A practical obstacle for sellers is that verifying and settling on-chain payments can introduce operational complexity (node providers, confirmations/finality strategy, chain-specific quirks, reorg considerations, etc.).
x402 implementations often introduce a facilitator component to handle:
- validating the payment payload
- broadcasting transactions (where needed)
- checking status/finality
- returning a standardized payment response to the seller/server
This lets a typical SaaS team add paid endpoints without becoming a blockchain infrastructure team.
Performance and Settlement Expectations
The x402 whitepaper frames a major advantage of on-chain rails as faster settlement and reduced chargeback-style risk compared to legacy payment rails, citing on-chain settlement in the ~200ms range in its discussion (often referenced with Base).
Treat that as an architectural aspiration for the end-to-end flow under ideal conditions; actual user experience will depend on network conditions, confirmation policy, and implementation choices.
Extensions That Matter in Real Deployments
The core x402 handshake is powerful, but production systems tend to need additional layers. The x402 docs ecosystem describes patterns such as:
1) Bazaar / discovery (agent-friendly marketplaces)
Discovery is a missing piece for agent commerce: how does an agent find payable tools/endpoints, understand their prices, and then call them?
x402 documentation includes guidance around discovery concepts so clients can search and select x402-enabled resources before paying.
2) Authentication + payment together
Even if payments work, many services still want user identity, subscription entitlements, or allowlists.
The broader x402 ecosystem discusses combining sign-in style proofs with payment fallback patterns so you can support both members and walk-up pay-per-call users in one workflow.
3) Idempotency (avoid accidental double charges)
Any retry protocol needs a strategy for safe retries. The x402 ecosystem includes explicit guidance around retries and standardized flows (notably in V2 docs and MCP server patterns).
In production, you want a clear idempotency policy so repeated requests don’t create repeated charges.
Where x402 Is Used: High-Value Use Cases
x402 is most compelling when you want granular monetization and automation-friendly billing:
- Paid APIs and data feeds: pay per request, per query, or per unit of data
- AI tool usage
- Agents buying search, scraping, enrichment, inference, or execution tools
- Cloudflare specifically references x402 support in its Agents ecosystem and MCP server context, which is aligned with agent workflows.
- Paywalled content: small payments for access, with no account creation
- Serverless and compute primitives: metering compute-like actions into paid HTTP calls (an area infrastructure providers are exploring conceptually).
Security and Abuse: What You Must Design For
x402 gives you a payment handshake, but you still need to engineer for real-world failure modes.
Replay and double-spend risk at the application layer
Because clients may retry requests, you need a strategy to ensure the same payment proof can’t be replayed to get multiple deliveries (or that repeated deliveries are acceptable by design).
Using idempotency identifiers and server-side deduplication is a standard solution pattern in paid request flows.
Pricing integrity and request binding
You want to bind what the client is buying to the requirement you issued:
- route + method
- key request params (if applicable)
- price + asset + network + recipient
Otherwise, a client might try to reuse a cheaper requirement against a more expensive request.
The Coinbase repo’s typical flow explicitly frames selection of payment requirements and creation of payloads based on scheme/network, which is where robust binding logic typically lives.
Denial of service and spam economics
402 endpoints can be spammed. You still need standard web defenses:
- rate limiting
- bot protection
- caching 402 responses where safe
- monitoring and abuse heuristics
Cloudflare’s interest here is not accidental: it lives at the edge where these concerns are acute.
Implementation Checklist (Practical and LLM-Friendly)
If you’re a seller (API/content provider)
- Decide which endpoints are payable and define pricing units (per request, per dataset, per compute unit).
- Return 402 + PAYMENT-REQUIRED on unpaid calls with at least one valid payment option.
- Accept retry requests carrying PAYMENT-SIGNATURE.
- Verify + settle using:
- your own verification logic, or
- a facilitator to reduce chain complexity.
- Return 200 + PAYMENT-RESPONSE alongside the resource.
- Add idempotency controls for safe retries.
- Add observability: log requirement IDs, payment IDs, response codes, settlement statuses.
If you’re a buyer (client/app/agent)
- Implement 402 handling:
- parse PAYMENT-REQUIRED
- select compatible option (scheme/network/asset)
- create payment payload, sign it
- retry request with PAYMENT-SIGNATURE
- Implement retry limits, backoff, and clear failure modes (insufficient funds, unsupported network, invalid requirement).
- Secure key management (especially for autonomous agents):
- spending limits
- allowlists
- monitoring
Conclusion
x402 is best understood as a practical standard that makes payments a first-class part of HTTP: servers can price endpoints, clients can pay programmatically, and the web can support true pay-per-request economics, especially for APIs and AI agents.
If you’re evaluating it, the fastest way to get clarity is to prototype one paid endpoint, implement safe retry/idempotency behavior, and decide whether a facilitator model is the right operational tradeoff for your team
Read Next:
- AI Agents For Stablecoins In 2026
- Mastercard Stablecoin Pay In 2026
- The Machines Are Spending Stablecoins
FAQs:
1. Is x402 only for stablecoins or crypto?
No. In practice, many examples focus on stablecoins (because they’re programmable and settle quickly), but x402 is designed as an open standard around HTTP 402 with extensible payment methods. The public framing emphasizes crypto/stablecoins today because they fit agentic, API-native payments well.
2. Do I need a facilitator?
Not strictly. Facilitators are a common pattern to simplify verification and settlement for sellers. If you can verify and settle safely in-house, you can do that—just be prepared for chain ops complexity.
3. How does x402 avoid accounts and API keys?
The idea is that payment itself becomes the “gate.” If a request is paid, the server returns the resource. That’s why x402 is marketed as enabling monetization without accounts, sessions, or credential management—though you can still add auth layers on top when your use case needs it.
4. What happens if payment fails or is unsupported?
The client should treat it like any other failed requirement negotiation: select another compatible requirement (if offered) or surface a deterministic error (unsupported network, insufficient funds, invalid payload). The standardized headers make this failure handling automatable.
5. Is x402 mainly about AI agents?
Agents are a flagship use case because they need to purchase tools autonomously and frequently in small increments. That said, paid APIs, paywalled content, and developer tooling are equally natural fits. Cloudflare’s Agents SDK support is a strong signal of this direction.
Disclaimer:
This content is provided for informational and educational purposes only and does not constitute financial, investment, legal, or tax advice; no material herein should be interpreted as a recommendation, endorsement, or solicitation to buy or sell any financial instrument, and readers should conduct their own independent research or consult a qualified professional.